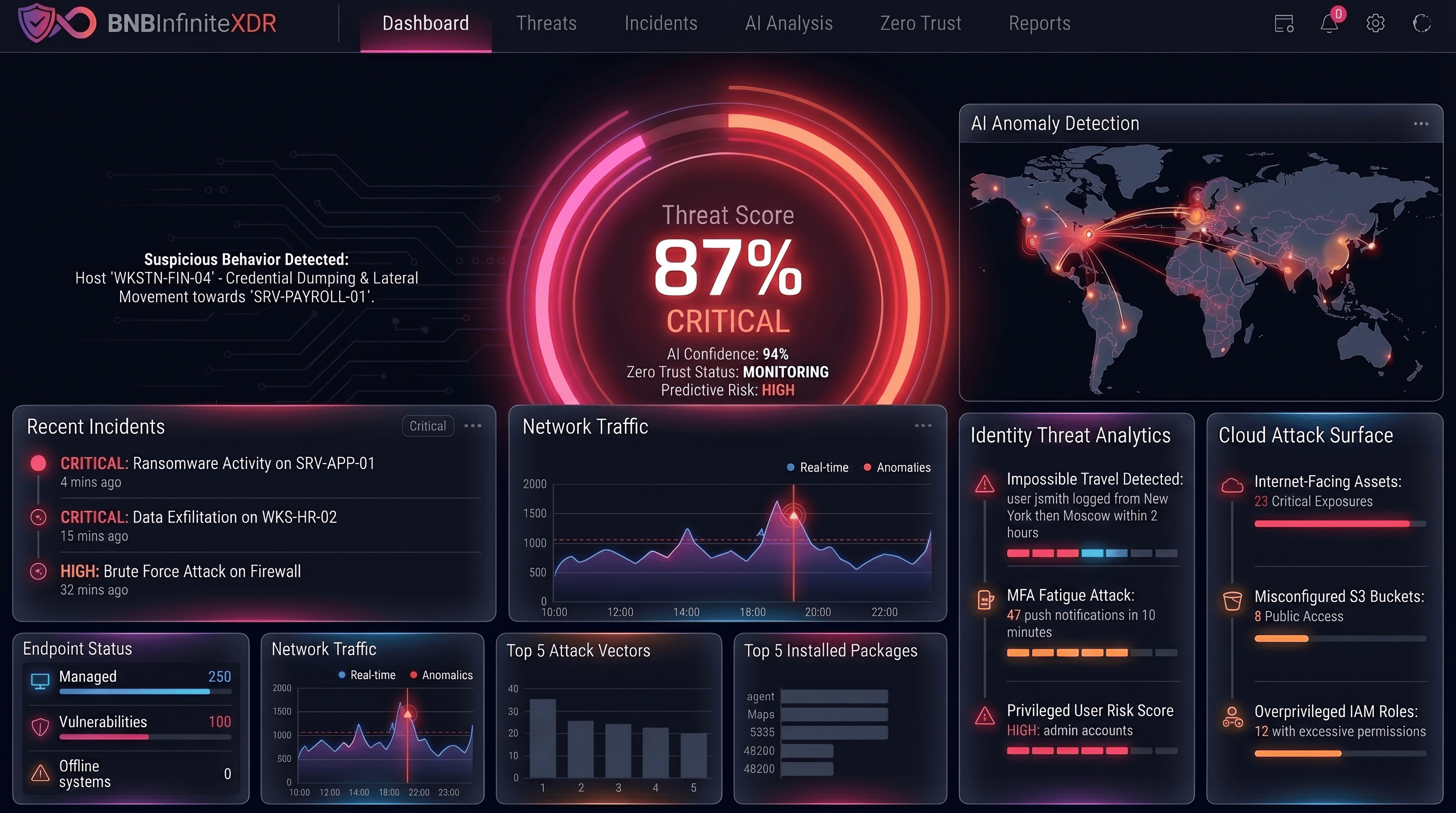
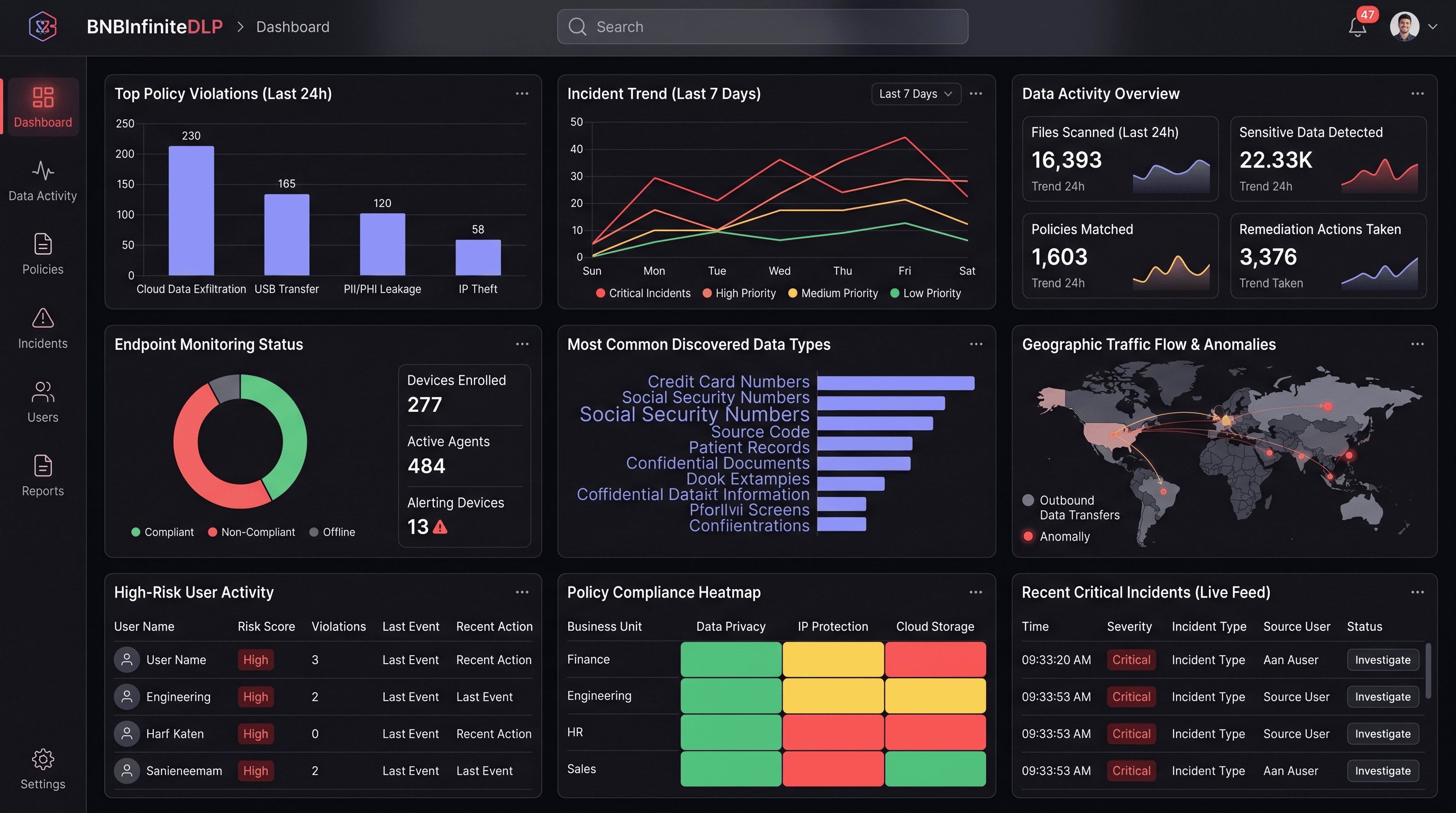
$4.4M ransom paid in 24 hours — from one forgotten credential.
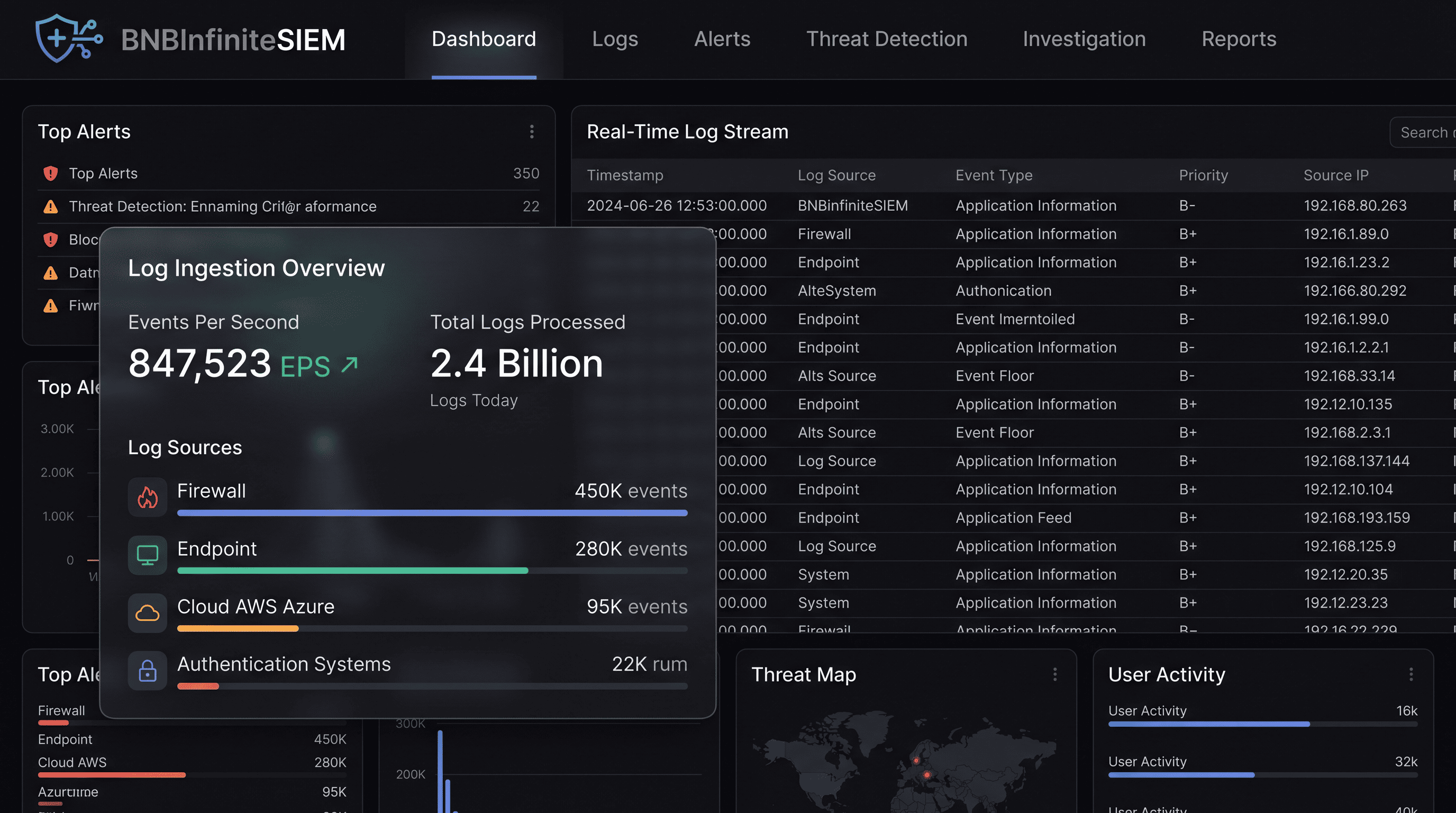
Attackers accessed a legacy VPN account dormant for six months — no MFA enforced, no anomaly alert raised. The identity tool never talked to the SIEM. By the time anyone responded, 100 GB had been exfiltrated and 10,000 endpoints were encrypted.