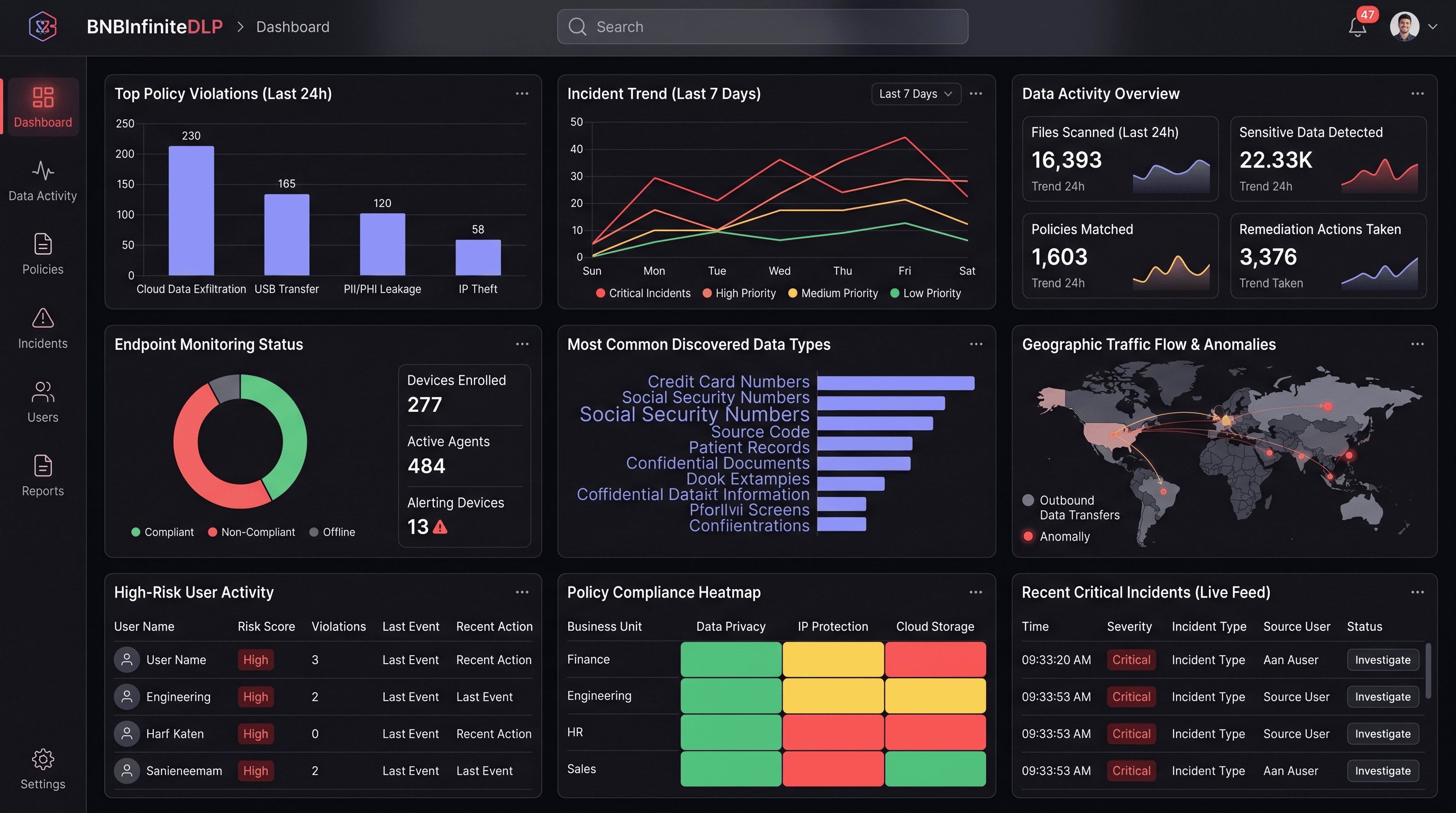
Stop data leaks
before they start.
BNB Infinite DLP discovers and classifies sensitive data across endpoints, email, cloud apps, and SaaS — then enforces policy the moment data moves, with ML-powered accuracy that eliminates the false positives that make legacy DLP teams disable their own tools.
Trusted by security-first teams at
Legacy DLP creates friction without delivering protection
First-generation DLP tools were built around rigid regex patterns and single-channel enforcement. The result is high false-positive rates that break business workflows — and blind spots that sophisticated threats exploit.
Channel blindness creates exploitable gaps
Email DLP can't see cloud sharing. Cloud DLP can't see USB. Web DLP misses browser-based SaaS uploads. Sophisticated insiders know exactly which channels go unmonitored.
False positives destroy analyst trust
Pattern-matching engines fire on every email address, every phone number in a contact book. After weeks of noise, analysts disable policies — eliminating protection along with the friction.
Classification drift leaves sensitive data exposed
Manual tagging rots as data moves between systems. Files tagged correctly at creation are re-shared, copied, and transformed into unclassified versions that policies never touch.
User friction drives shadow IT adoption
Heavy-handed blanket blocks interrupt legitimate work. Users find workarounds — personal email, consumer cloud storage, USB drives — and security loses all visibility.
No visibility into insider pre-exfiltration
Departing employees stage data for weeks before exfiltration. Legacy DLP detects the final transfer but misses the months of preparation that preceded it.
Compliance evidence is manual and fragmented
Without automated evidence collection, proving data protection compliance requires manually assembling enforcement logs, policy configurations, and exception records across multiple systems.
Content-aware, context-smart data protection.
Classification that understands meaning, not just patterns. Enforcement that evaluates intent, identity, device, and destination — not just the content of a file.
ML classification at 98% accuracy
Models trained on your data types classify PII, PHI, secrets, and IP by content and context — handling OCR, code snippets, and images that regex-based engines miss entirely.
One policy, every channel
The same classification engine and policy set enforces consistently across endpoints, email, web browsers, cloud apps, and SaaS — with no channel-specific rule duplication.
Pre-exfiltration detection
UEBA signals surface data hoarding, unusual download spikes, and staging patterns weeks before exfiltration occurs — giving security teams time to investigate before damage is done.
Employee-friendly enforcement
Soft prompts explain why content is sensitive and offer approved alternatives — fewer hard blocks means fewer workarounds, shadow IT, and angry helpdesk tickets.
Continuous policy validation
DLP policies run against synthetic test data every 24 hours. Misconfigurations, coverage gaps, and policy drift surface in dashboards before a real incident exposes them.
Legal hold & eDiscovery
When legal needs evidence, DLP's immutable evidence vault surfaces the exact version of every file that left the organisation — timestamped, hashed, and chain-of-custody preserved.
Discover, classify, enforce, and prove — continuously
Discover
Automated crawlers scan endpoints, email repositories, cloud storage, and SaaS applications to build a comprehensive map of where sensitive data lives across your entire environment.
Everything DLP needs to be — built in.
Purpose-built capabilities that work together on one data fabric — not eight separate tools you have to integrate.
ML-powered content classification
Identifies sensitive data by meaning and context — not just regex patterns. Handles structured data, unstructured documents, code, images, and OCR-extracted text from screenshots and scanned files.
360° channel coverage
Single policy engine enforces consistently across endpoint file activity, email attachments, web browser uploads, cloud storage sharing, SaaS application actions, and USB removable media.
Insider risk & pre-exfiltration detection
UEBA integration surfaces anomalous data download spikes, bulk email forwarding, unusual cloud sync activity, and staging patterns that precede exfiltration by weeks.
Built different.
What sets BNB Infinite DLP apart from channel-specific tools
A single classification engine across every channel means consistent enforcement and no exploitable seams.
See it in actionContext beats content-only detection
The enforcement decision considers who is sending, from what device, to which destination, at what risk level — not just what the file contains. That's why our false-positive rate is 85% lower.
DLP evidence feeds GRC automatically
Every DLP enforcement action flows to the GRC module as compliance evidence. The same event that stopped a data leak satisfies your GDPR Article 32 control — simultaneously.
Fused with XDR for incident escalation
When DLP detects a high-risk exfiltration attempt, it automatically creates a correlated XDR incident with full context — identity, endpoint state, data sensitivity, and behavioral history.
Built for every security reality
Real deployment scenarios from security teams across financial services, healthcare, SaaS, and government — with the outcomes they achieved.
GDPR & HIPAA enforcement
Automatically detect and block PII and PHI from leaving approved boundaries across every channel — with a continuous evidence trail that satisfies regulatory requirements.
- PII/PHI detected across all 6 major channel types
- Automated evidence satisfies GDPR Article 32
- Policy evaluation in <5ms — zero user friction
Source code exfiltration prevention
Detect and block code pushed to personal repositories, pasted to public pastebins, attached to personal email, or copied to USB drives by employees and contractors.
- Git push monitoring to unapproved destinations
- Pastebin and code-sharing site blocking
- Contractor offboarding data movement detection
Insider risk programs
Identify high-risk individuals through behavioral data access signals weeks before exfiltration occurs — with investigation workflows that preserve HR privacy requirements.
- Pre-exfiltration staging detected 3–6 weeks early
- Cross-system behavioral correlation (files + email + SaaS)
- Privacy-gated investigation workflow for HR alignment
M&A and contractor data governance
Enforce precise data-sharing boundaries with external parties — watermark sensitive documents, monitor access, and detect boundary violations in real time.
- Watermarking with entity-specific tracking
- Real-time violation alerts with full context
- Automatic evidence export for legal proceedings
Cloud migration data protection
Monitor and control sensitive data movement during cloud migrations — ensuring regulated data doesn't land in non-compliant storage tiers or regions.
- Data residency violations detected in real time
- Classification coverage during migration window
- Compliance verification reports at migration close
Zero-trust data access enforcement
Enforce data access policies based on device health, identity posture, and classification label — a foundational layer of any zero-trust architecture.
- Device health integrated into policy decisions
- Identity-aware enforcement across all channels
- Continuous posture verification, not point-in-time
Classification accuracy
ML models trained on customer data types, not generic patterns.
Read case studiesContext-aware enforcement reduces analyst noise dramatically.
Users experience no friction on legitimate transfers.
Every enforcement action logged as compliance evidence automatically.
Connects to everything
your team already uses
8+ native connectors. No custom pipelines, no professional services required.
Outcomes from teams like yours
“The unified DLP and SIEM integration caught data exfiltration attempts we were completely blind to with our previous tooling. A departing engineer had been staging source code for 11 days — BNB caught it on day three and surfaced it as an XDR incident with full context.”
Sarah Chen
Chief Information Security Officer · HealthSecure Inc
“We went from a false-positive rate that made our DLP effectively useless to one our team actually trusts. Our policy coverage expanded threefold after the migration because analysts stopped disabling rules to avoid the noise.”
Omar Hassan
Director, Data Protection · GlobalRetail Group
Frequently asked questions
Everything you need to know before making the decision.
Protect data everywhere it moves — without slowing your team.
See how BNB Infinite DLP replaces regex-era data protection with content-aware, context-smart enforcement across every channel simultaneously.