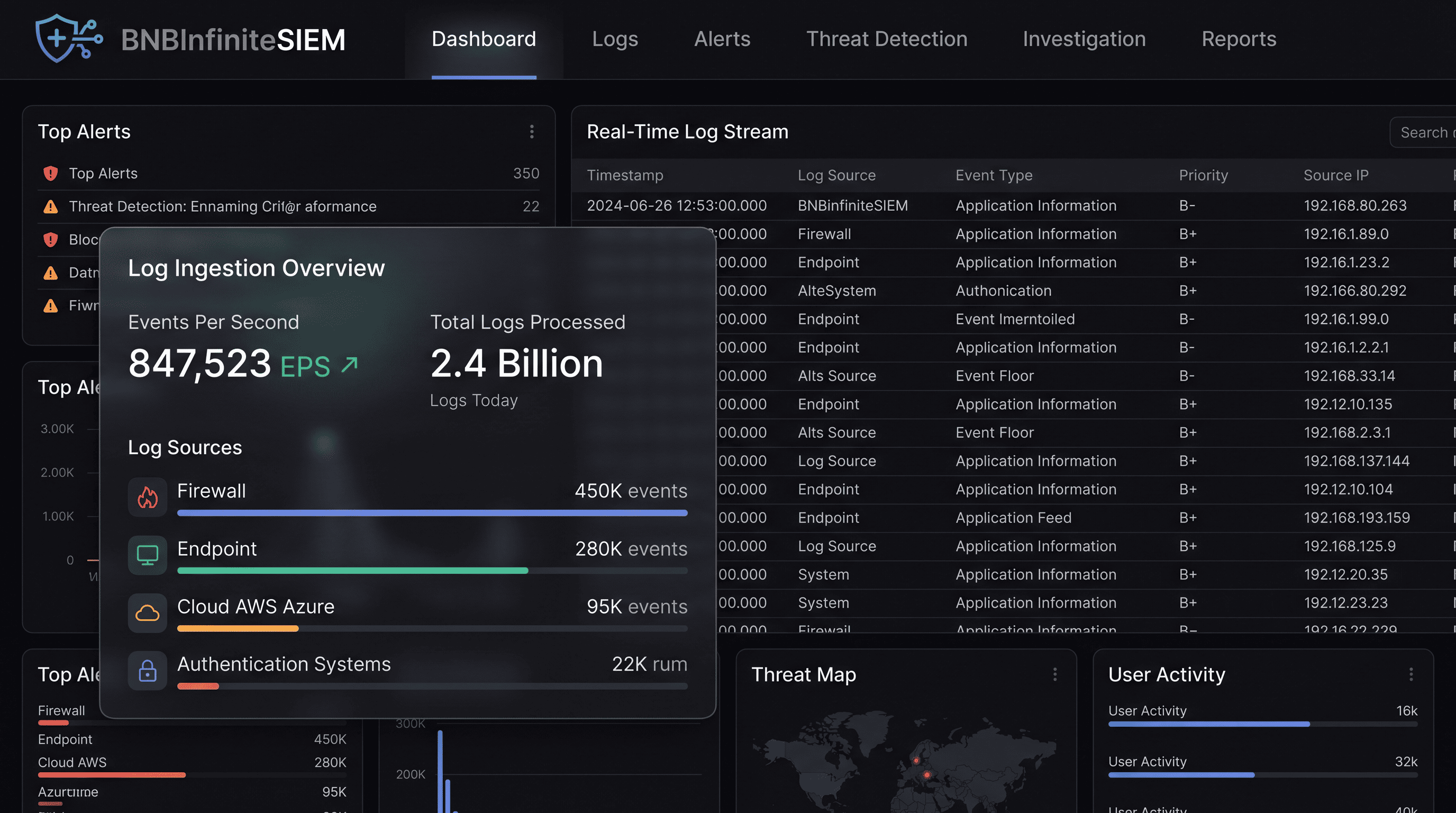
Correlate billions of events.
Surface the 10 that matter.
BNB Infinite SIEM ingests petabytes of logs from 120+ sources, normalizes them with OCSF at ingest, and runs 2,900+ managed detection rules — replacing alert floods with high-confidence, actionable incidents your analysts can actually investigate.
Trusted by security-first teams at
Legacy SIEMs were built for storage, not detection
Traditional SIEM platforms became expensive log archives with brittle correlation rules. The result: massive alert volumes, slow queries, and analysts buried in noise they can't act on.
Alert fatigue destroys analyst trust
Rigid detection rules fire indiscriminately. After weeks of false positives, analysts learn to ignore the alert queue — including the real incidents hidden inside it.
Petabyte queries take hours
Legacy architectures weren't built for cloud-scale data volumes. Investigations grind to a halt while analysts wait for query results across 3-day windows.
Coverage gaps at the seams
On-prem SIEMs miss cloud-native events. Cloud SIEMs miss on-prem telemetry. Attackers have memorized which seams go unmonitored.
Rule debt compounds over time
Hundreds of noisy custom rules nobody dares touch accumulate over years. False positives that have fired daily for three years sit untouched because no one owns them.
Normalize-at-query costs you time
Schema inconsistencies across data sources force analysts to parse, translate, and reformat at query time. Every investigation starts with housekeeping instead of threat hunting.
Storage costs scale faster than value
Legacy pricing models charge per GB ingested, incentivizing teams to exclude data sources — creating the very blind spots attackers exploit.
A detection-first SIEM engineered for petabyte-scale threats.
One platform ingests everything, normalizes at the wire, and applies 2,900+ managed detection rules continuously — so your analysts see incidents, not events.
Normalize once at ingest
OCSF schema applied at the point of ingestion across all 120+ sources. Every analyst query hits one consistent field set — no source-specific syntax, ever.
Managed detection, zero rule debt
2,900+ rules maintained by our detection engineering team. New coverage ships as threats emerge. You never touch a rule to keep detection current.
Petabyte queries in seconds
Hot/warm/cold tiered data lake built on open formats. 90-day windows query in under 10 seconds. Sub-second pivot from alert to full context.
AI-generated incident summaries
Every alert arrives with an AI-authored summary: what happened, which assets are involved, confidence score, and recommended next actions — drafted before the analyst opens the ticket.
Schema-on-read normalisation
Ingest any format — Syslog, CEF, JSON, or proprietary — without building pipelines first. OCSF normalisation happens at query time, so you never delay collection waiting for a parser.
Compliance-first retention tiers
Hot: 90 days fully indexed. Warm: 1 year query-able. Cold: 7 years compressed archive — at a fraction of legacy SIEM storage cost, with no data loss on any tier.
From raw log to high-confidence incident
Ingest at scale
Stream logs, events, and telemetry from 120+ sources via pre-built connectors, native APIs, or syslog. No data excluded to control costs.
Everything SIEM needs to be — built in.
Purpose-built capabilities that work together on one data fabric — not eight separate tools you have to integrate.
120+ native source connectors
Pre-built integrations for every major cloud platform, endpoint security tool, identity provider, network device, and SaaS application. Deploy a new source in minutes, not weeks.
OCSF normalization at ingest
Open Cybersecurity Schema Framework applied at the point of collection across all sources. One query syntax for petabytes of heterogeneous data — no per-source translation required.
2,900+ managed detection rules
Continuously tuned detection library maintained by BNB Infinite's detection engineering team. New threat coverage deployed without configuration changes on your end.
Built different.
Why security teams migrate from legacy SIEMs to BNB Infinite
Detection-first architecture built for the data volumes, cloud footprints, and analyst realities of 2025 — not 2005.
See it in actionCost that scales with data, not against you
Open-format storage (Parquet + Iceberg) and tiered retention keep costs linear. No per-GB ingestion tax that incentivizes excluding data sources and creating blind spots.
Detection without the maintenance burden
2,900+ managed rules means zero rule debt. Our detection engineers track adversary technique evolution and ship updated coverage without touching your configuration.
One data lake for detection, response, and compliance
SIEM shares the same data fabric as XDR, DLP, and GRC. A log stored once serves detection, investigation, automated response, and compliance evidence — simultaneously.
Built for every security reality
Real deployment scenarios from security teams across financial services, healthcare, SaaS, and government — with the outcomes they achieved.
SOC modernization
Replace a legacy on-prem or first-gen cloud SIEM with a detection-first platform that scales with your cloud footprint and eliminates alert fatigue.
- Migration completed in 60 days average
- Alert volume reduced 90% on day one with managed rules
- Query performance 10× faster than legacy architecture
Compliance log management
Centralize all compliance-required log sources into one retention store that meets SOC 2, PCI DSS, HIPAA, and ISO 27001 mandates simultaneously.
- Unified log store for all 6 major frameworks
- 7-year retention with automatic tiering
- Auditor-ready evidence exports in one click
Proactive threat hunting
Run hypothesis-driven hunts across 90 days of full-fidelity telemetry with sub-second query response — no data sampling, no pre-aggregation loss.
- Sub-10-second queries on 90-day hot tier
- YARA, Sigma, and natural-language hunt support
- Inline pivot from hunt result to full incident context
Cloud security monitoring
Ingest CloudTrail, GCP Audit Logs, Azure Monitor, and Kubernetes audit logs alongside endpoint and network telemetry for unified cloud threat detection.
- Cloud-native ingestion with no agent required
- CSPM posture events correlated with SIEM telemetry
- Cloud-specific detection rules for 40+ attack patterns
Multi-cloud environments
Normalize and correlate telemetry from AWS, Azure, and GCP into a single detection surface — eliminating the need for separate SIEM instances per cloud.
- Single OCSF schema across all cloud providers
- Cross-cloud lateral movement detection
- Unified alert queue regardless of origin cloud
MSSP multi-tenant operations
Manage multiple client tenants from a single interface with strict data isolation, per-client detection tuning, and white-labeled reporting.
- Strict tenant isolation with zero data bleed
- Per-client detection rule sets and tuning
- Automated SLA reporting per tenant
Events processed monthly
No sampling. No data exclusion. Complete telemetry coverage.
Read case studiesAI correlation vs. raw rule-based alert counts.
Vs. legacy SIEM architecture on equivalent data volumes.
2,900+ managed rules updated continuously by our team.
Connects to everything
your team already uses
8+ native connectors. No custom pipelines, no professional services required.
Outcomes from teams like yours
“We replaced two legacy SIEMs with BNB Infinite and query times dropped from 20 minutes to under 10 seconds. The managed rules library alone saved us three FTEs worth of detection engineering time annually.”
Priya Sharma
Director of Security Engineering · CloudScale Inc
“The migration was the fastest infrastructure change I've overseen in 15 years. We were ingesting production telemetry within 48 hours and running our first correlated detections on day four. The OCSF normalization is genuinely transformative.”
David Kowalski
Chief Information Security Officer · NorthBridge Financial
Frequently asked questions
Everything you need to know before making the decision.
Ready to replace alert noise with real incidents?
See how BNB Infinite SIEM brings detection-first log management, petabyte-scale queries, and zero rule debt to your entire environment.