From first signal to
contained threat.
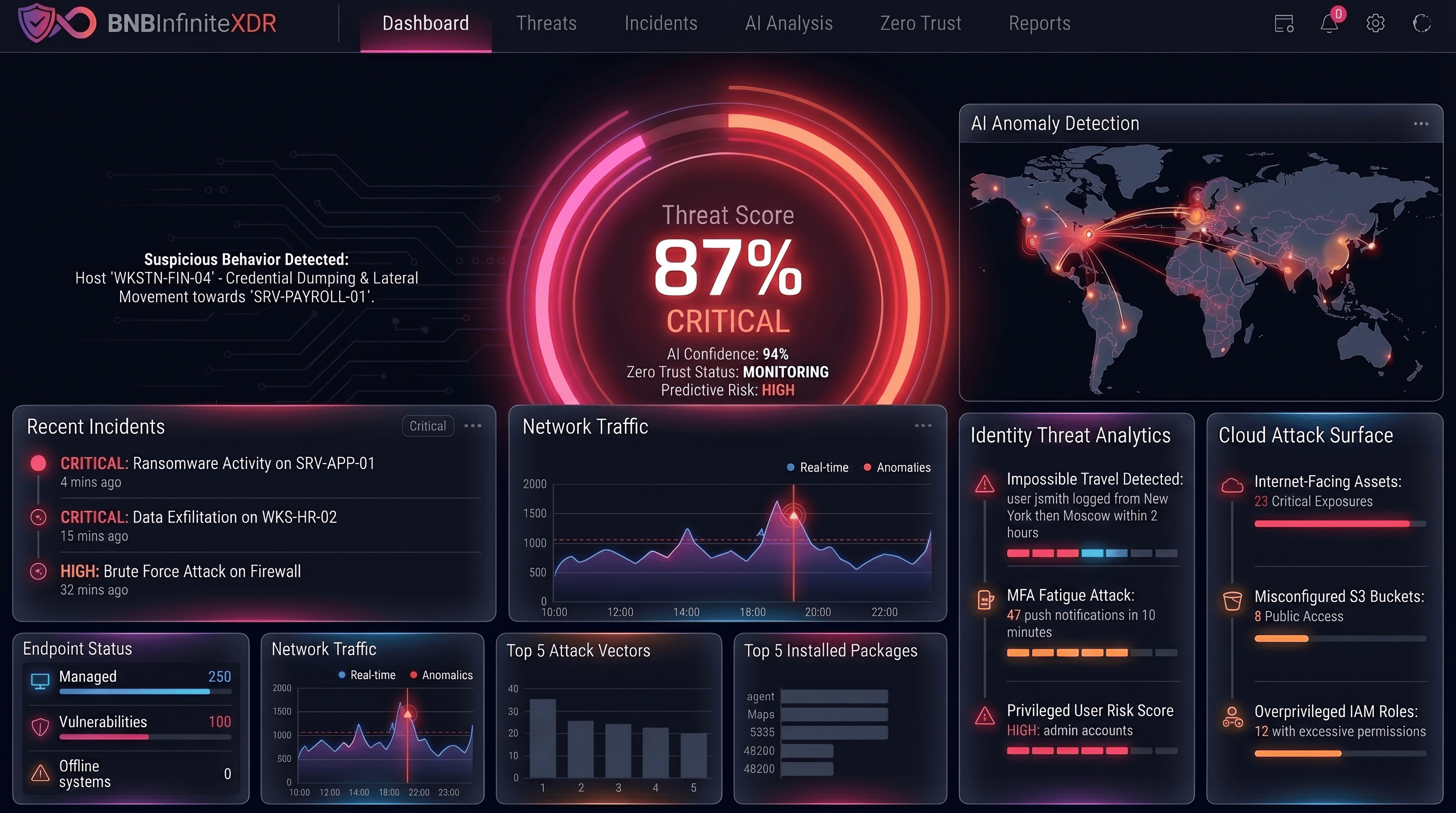
BNB Infinite XDR correlates endpoint, identity, cloud, and network telemetry into a single guided investigation. Automated playbooks execute containment in minutes — with guardrails, approvals, and a full immutable audit trail on every action.
Trusted by security-first teams at
Detection without unified response is just noise
Modern attacks don't stay in one tool's lane. They traverse endpoints, identity systems, cloud workloads, and SaaS apps — yet most teams still investigate across six siloed consoles.
Tool sprawl kills investigation speed
Pivoting between endpoint, identity, cloud, and network tools turns a 10-minute investigation into a 4-hour marathon of manual correlation.
Lateral movement goes unseen
Without cross-domain visibility, attackers move laterally for months. By the time one tool alerts, damage is already done in another.
Playbooks don't scale
Copy-paste runbooks and human-speed containment let adversaries persist, escalate privileges, and encrypt data while analysts work step by step.
Alert volume overwhelms teams
Without correlation, every raw signal fires independently. Critical incidents are buried under thousands of low-fidelity alerts that analysts learn to ignore.
Cloud workloads are a blind spot
Container and serverless workloads operate outside traditional detection scope. Attackers exploit cloud-native attack paths that on-prem tools can't see.
No audit trail for response actions
Ad-hoc containment leaves no record. When auditors or regulators ask what was done and when, manual response teams can't answer.
One investigation surface. Automated containment.
XDR stitches every telemetry source into a single timeline, scores threats by blast radius, and executes response playbooks at machine speed — with every action logged automatically.
Unified telemetry fabric
Endpoint, cloud, identity, and network signals share one schema. Cross-domain correlation happens automatically — no manual pivoting between consoles.
Response at machine speed
Automated playbooks execute isolate, revoke, quarantine, and notify in seconds — with guardrails and approval workflows you fully control.
Explainable AI decisions
Every correlation shows its reasoning chain: which signals fired, which rules matched, which entities are linked. Analysts trust it because they can verify every step.
Zero-trust containment
Enforcement doesn't just alert — it acts. Session revocation, lateral movement blocking, and least-privilege enforcement execute across identity and endpoint simultaneously.
90-day forensic memory
Full un-sampled telemetry retained for 90 days in hot tier. Sub-10-second queries across any endpoint, user, or time window — nothing downsampled, nothing lost.
Continuous coverage validation
Built-in breach simulation tests your detection against 300+ MITRE ATT&CK techniques weekly — so you know exactly what you catch before an attacker finds what you miss.
From raw signal to resolved incident — in minutes
Ingest & correlate
All telemetry streams into the unified data fabric. AI links related signals across domains into a single high-fidelity incident automatically.
Everything XDR needs to be — built in.
Purpose-built capabilities that work together on one data fabric — not eight separate tools you have to integrate.
Cross-domain signal correlation
AI-driven correlation across endpoints, cloud workloads, identity providers, and network traffic. Related signals become one high-confidence incident, not dozens of separate alerts.
Behavioral analytics (UEBA)
Continuous baseline of every user, device, and workload. Deviations from normal — unusual login times, atypical data access, impossible travel — surface as prioritized risk signals.
AI-guided investigation workspace
Attack timeline, blast radius, root cause, and recommended next steps generated automatically for every incident. Analysts start mid-investigation, not from zero.
Built different.
Why XDR teams choose BNB Infinite over point solutions
The difference between stitching tools together and building on a unified fabric shows up in every investigation.
See it in actionOne schema, zero correlation tax
Every module shares the same OCSF data fabric. There's no ETL, no schema translation, no re-ingestion between XDR and SIEM. That's nanoseconds, not minutes.
Response with a compliance trail
Every automated and analyst action is immutably logged with timestamps, approvals, and reasoning. Your XDR response is your compliance evidence — automatically.
No black boxes, ever
Every AI correlation decision exposes its evidence chain. Analysts see which signals fired, which rules matched, and why the system scored it high. Trust through transparency.
Built for every security reality
Real deployment scenarios from security teams across financial services, healthcare, SaaS, and government — with the outcomes they achieved.
Ransomware early detection
Detect lateral movement, credential abuse, and staging behavior hours before encryption begins — and contain it before a single file is encrypted.
- Lateral movement detected in <4 min average
- Automatic host isolation on confirmed threat
- Full evidence trail from first signal to containment
Insider threat investigation
Correlate user behavior across endpoints, SaaS applications, email, and data access into a single timeline with clear intent signals.
- UEBA baseline surfaces deviation within 24hr
- Cross-channel correlation: email + endpoint + data
- Privacy-safe investigation with role-gated access
Cloud account takeover
Detect impossible travel, unusual API call patterns, privilege escalation, and anomalous resource creation in real time across AWS, Azure, and GCP.
- Cloud-native signal ingestion with no agents
- Anomalous IAM activity flagged in real time
- Automated token revocation playbook available
Supply chain attack hunting
Hunt proactively across 90 days of full telemetry for indicators of supply chain compromise — before an alert fires.
- Sub-10-second search across 90-day hot tier
- Custom YARA and Sigma rule deployment
- Cross-customer threat sharing (anonymized)
Zero-day exploitation response
When a new CVE drops, deploy coverage, hunt for exploitation indicators, and contain affected systems faster than your adversary can pivot.
- New rule coverage deployed in <4 hours of CVE publication
- Retroactive hunt across historical telemetry
- Automated blast-radius scoping for prioritized response
M&A security due diligence
Gain full visibility into an acquired entity's security posture and active threats within days of onboarding their telemetry.
- Telemetry onboarding in 72 hours
- Immediate detection coverage for acquired environment
- Executive risk dashboard for board reporting
MTTR reduction
From multi-hour investigations to under 15 minutes on average.
Read case studiesUnified console eliminates tool-switching overhead.
AI correlation filters noise before it reaches the analyst queue.
Every response step immutably recorded for compliance.
Connects to everything
your team already uses
8+ native connectors. No custom pipelines, no professional services required.
Outcomes from teams like yours
“BNB Infinite XDR collapsed a 4-hour investigation into 12 minutes. The cross-domain correlation surfaces context we simply couldn't see before — endpoint activity, identity events, and cloud API calls unified in one timeline.”
Arjun Patel
Head of Security Operations · FinTech Corp
“We decommissioned three separate detection tools in the first 90 days. The savings funded two additional security analysts and we still came out ahead on coverage. The unified playbook engine alone was worth the migration.”
Leila Nazari
VP Engineering & Security · CloudScale AI
Frequently asked questions
Everything you need to know before making the decision.
Detect faster. Contain smarter. Prove everything.
See how BNB Infinite XDR replaces your SOC's tool sprawl with a single detection and response fabric — with a live walkthrough of your hardest use case.